When it comes to avoiding risk, what is OneNeck doing?

Security is intrinsic to our services (for all customers) and organization (all the way to the president and CEO of our parent company TDS Inc.). It’s part of every service we develop—from start to finish. Additionally, we leverage the Critical Security Controls (CSC), outlined by the Center for Internet Security (CIS), to complete our annual security assessments and third party audits.
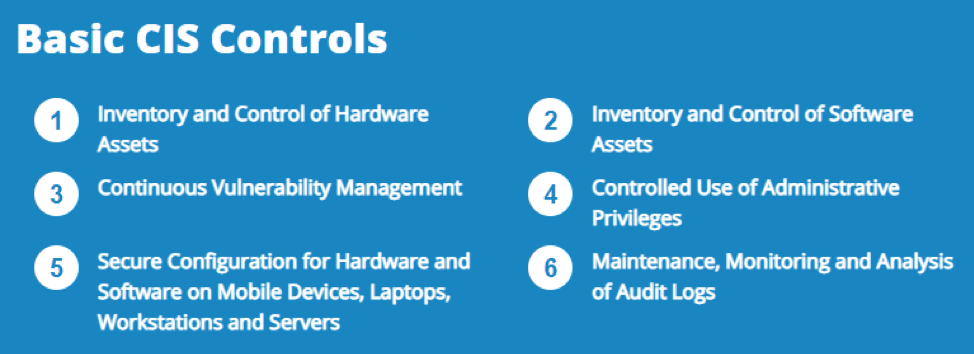
The Critical Security Controls provide a series of cybersecurity actions prioritized by their criticality in preventing cyberattacks. In particular, the first six controls (referred to as the Basic Control set, see below) focus on cybersecurity “hygiene.” Studies show that implementation of these first six CIS Controls provides an effective defense against about 85 percent of the most common cyberattacks.
The OneNeck Security team focuses on providing timely input into developing new services, securing current IT infrastructure and systems so customers can rest assured we are ready and able to meet demands for secure services.
Internally, we establish practices in alignment with the critical security controls. It’s important we follow the advice and recommendations we give customers in order to demonstrate quick and effective ways we’re prepared to address aspects of the Critical Security Controls.
Customers count on us to have a rigorous security framework in place and to submit to outside resources to audit our work. Having third-party vendors perform internal audits (just like we do for SSAE, HIPPA, etc.), provides verification we have the evidence in place we claim to, therefore, avoiding potential bias.
To begin assessing the broad scope of security and compliance needs your business faces, our virtual Chief Information Security Officer (vCISO) service can help. With the help of our have team, comprised of security experts who stay current on emerging threats, you can bypass the hassle of hiring an in-house CISO and immediately bring in the security leadership you need to assess and improve your overall security posture.



